Why Your Security Policy Can’t Afford to Ignore Office Technology
Document Management | Managed IT | Office Copiers, Printers, and MFPs | Office Technology | Pro AV | Security Solutions
A security policy that covers servers and laptops but ignores printers, document workflows, and physical access controls is not a complete security policy. Every device, every workflow, and every point where information moves must be part of a single, coherent strategy.
LDI Connect partners with organizations to build unified security architectures that span print environments, document management, cloud services, MSSP-delivered security operations, AI-powered compliance management, and physical security, integrated and continuously monitored.
How Has the Threat Landscape Changed?
Attacks are no longer exclusively the work of individual bad actors probing for obvious vulnerabilities. Today’s threat environment is characterized by AI-driven attacks, automated reconnaissance, adaptive malware, AI-generated phishing campaigns virtually indistinguishable from legitimate communications, and ransomware-as-a-service operations deployable against targets of any size.
At the same time, the regulatory environment has grown significantly more complex. Depending on your industry and geography, your organization may be subject to HIPAA, SOC 2, PCI-DSS, CMMC, GDPR, CCPA, or other frameworks, each with its own requirements around data handling, access controls, audit trails, and incident response.
This is precisely why the Managed Security Services Provider (MSSP) model has become the standard of care for organizations that take security seriously. An MSSP delivers a dedicated security operations capability integrated with your full technology ecosystem.
Why Are Office Printers a Security Risk?
Printers are often overlooked, but they present multiple entry points for attackers across both hardware and network layers.
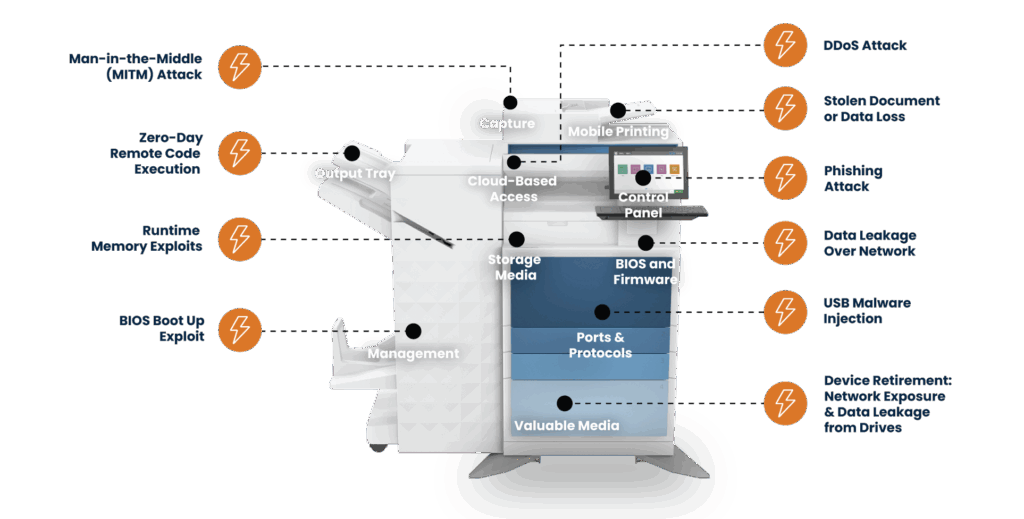
Think about what flows through a typical office multifunction device (MFD) on any given day, HR documents, legal contracts, financial statements, patient records, and confidential communications. These devices are not passive hardware, they are intelligent network endpoints with hard drives, memory, and sophisticated software.
Left unmanaged, MFDs represent a significant vulnerability and potential compliance liability. Secure print solutions change that equation entirely.
- Print jobs are held in a secure queue and released only upon authentication
- Authentication options include proximity card, PIN, or biometric verification
- Documents never sit uncollected in output trays
- All print activity is logged, auditable, and reportable
- AI-driven analytics can detect and flag anomalous behavior in real time
For organizations operating within Microsoft 365 environments, print security integrates directly with Azure Active Directory, extending identity governance to print infrastructure.
How Does Document Management Fit Into a Security Architecture?
In a modern workflow, the MFD becomes an input device, where physical documents enter structured, secure, and compliant digital processes.
AI-powered document recognition platforms automatically classify documents at the point of capture and apply handling rules without manual intervention.
- Sensitive data is routed to the correct system automatically
- Retention policies are applied at capture
- Access controls and encryption are enforced consistently
- Every document interaction is logged and audit-ready
This eliminates human error and ensures consistent compliance with data handling policies.
What Does an MSSP Provide That Internal IT Cannot?
For most organizations, building a full-scale internal security operations capability is not feasible. Talent is scarce, tools are complex, and compliance demands continuous monitoring.
An MSSP provides 24/7/365 monitoring across networks, endpoints, cloud environments, identity systems, and print infrastructure.
- Continuous threat detection and response
- Real-time incident triage and mitigation
- Ongoing compliance monitoring and reporting
- Automated evidence collection for audits
- Unified control frameworks across multiple regulations
How Is AI Used in a Unified Security Architecture?

AI is both a threat enabler and a powerful defensive tool. Within a unified environment, it delivers value across several areas:
Intelligent Threat Detection
AI correlates signals across systems to detect threats that isolated tools would miss.
Automated Compliance Monitoring
AI evaluates control environments against regulatory frameworks and identifies gaps in real time.
AI-Powered Document Classification and Data Loss Prevention
AI ensures sensitive information is identified and handled according to policy, preventing unauthorized sharing.
Predictive Security Posture Management
AI identifies vulnerabilities before they are exploited and prioritizes remediation based on real risk.
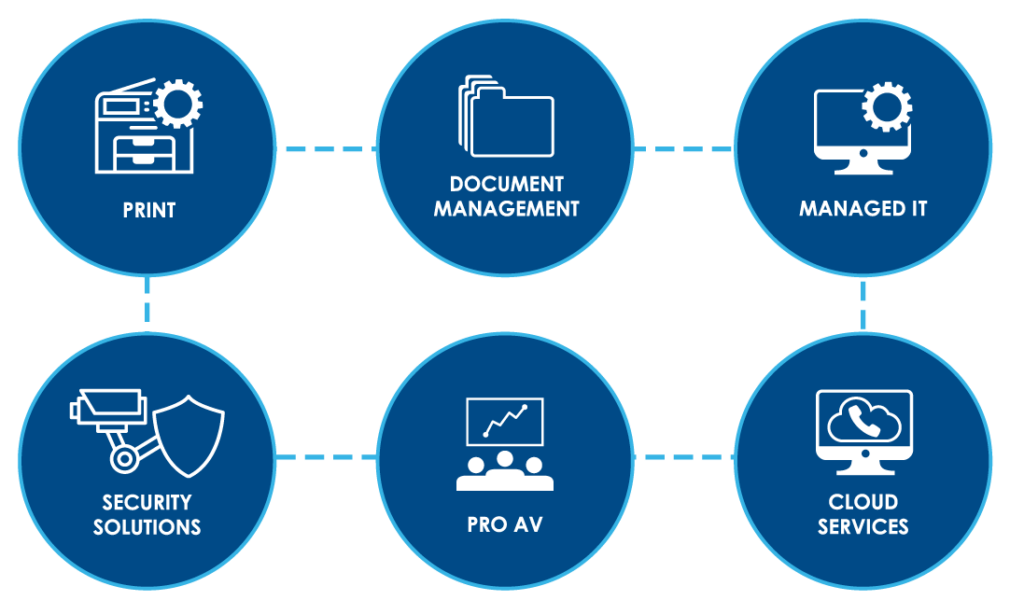
What Does a Complete, Unified Security Policy Look Like?
Security gaps often exist because systems are managed in silos. A modern policy must reflect how interconnected these environments truly are.
- Print & Managed Print Services: Device security, firmware management, and audit trails
- Document Management: AI-driven classification and controlled workflows
- Managed IT & Security: Threat detection, endpoint protection, and continuity planning
- Cloud Services: Secure access across all devices and locations
- Pro AV: Integrated emergency communication systems
- Physical Security: Surveillance and access control tied to identity systems
Frequently Asked Questions
As organizations begin to evaluate their current security posture, a few common questions tend to come up:
Do small businesses really need a unified security architecture?
- Yes. Smaller organizations are often targeted due to fragmented security. A unified approach strengthens resilience.
How does secure print integrate with compliance frameworks like HIPAA?
- Secure print platforms generate audit logs that satisfy compliance requirements and support continuous monitoring.
Is AI-driven security only for large enterprises?
- No. Cloud-native platforms scale to organizations of all sizes and improve over time.
How do I know if my current security policy has gaps?
- Gaps typically exist between systems, print, IT, cloud, and compliance. An assessment can identify them quickly.
What is the business case for investing in a unified security architecture?
- Organizations benefit from reduced downtime, simplified compliance, and stronger protection against evolving threats.
Ready to Build a Unified Security Architecture?
LDI Connect partners with organizations of all sizes to design and implement integrated office technology ecosystems, from managed print and secure document workflows to MSSP-delivered security operations, AI-powered compliance management, and physical security solutions.
Contact your LDI Connect Account Representative or schedule an assessment.